Vendor Risk Assessment Template: Free Checklist & Scoring Guide
Download a free vendor risk assessment template with scoring matrix. Covers financial, operational, compliance, cybersecurity, and reputational risk categories for procurement teams.
Introduction
Every vendor relationship carries risk. The question isn't whether your vendors will introduce problems — it's whether you'll see those problems coming before they become crises. A data breach at a technology vendor. A key supplier filing for bankruptcy. A compliance lapse that triggers regulatory scrutiny. These aren't hypothetical scenarios — they happen to organizations every day.
Yet most procurement teams still assess vendor risk informally, if at all. They rely on gut feel, surface-level questionnaires, and the occasional Google search. The result? Blind spots that turn into expensive surprises.
After 15+ years advising enterprises on vendor management, I've developed a structured vendor risk assessment framework that covers every category that matters. In this guide, I'm sharing the complete template — scoring matrix, category-specific checklists, and automation strategies — so your team can implement a rigorous risk assessment process immediately.
What you'll get from this guide:
- A clear definition of vendor risk assessment and why it matters
- Five risk categories every assessment must cover
- A complete scoring matrix template (1-5 scale) ready to use
- Category-specific checklists with actionable evaluation criteria
- Strategies for automating risk assessments with vendor portal technology
What Is a Vendor Risk Assessment?
A vendor risk assessment is a structured evaluation of the potential risks that a third-party vendor introduces to your organization. It examines a vendor's financial health, operational capabilities, regulatory compliance, cybersecurity posture, and reputation to determine whether the relationship is acceptable, manageable, or too risky to pursue.
Why It Matters More Than Ever
The scale of third-party risk is growing:
- The average enterprise relies on 250+ vendors for critical operations
- 62% of data breaches originate from third-party vendors
- Regulatory bodies increasingly hold organizations accountable for their vendors' failures
- Supply chain disruptions cost companies an average of $184 million per event
Without structured risk assessment:
- ❌ A vendor's data breach exposes your customers' data — you bear the regulatory fallout
- ❌ A key supplier's financial collapse halts production with no backup plan
- ❌ A vendor with poor security practices becomes the entry point for a cyberattack
- ❌ A vendor involved in ethical controversies drags your brand into the headlines
With structured risk assessment:
- ✅ Informed decisions about which vendors to engage, monitor, or avoid
- ✅ Early warning indicators that trigger intervention before problems escalate
- ✅ Defensible due diligence that satisfies auditors and regulators
- ✅ Stronger negotiating position when you understand a vendor's risk profile
When to Conduct Vendor Risk Assessments
Risk assessment isn't a one-time exercise. It should happen at multiple points:
- Pre-qualification — Full assessment as part of vendor selection, before contracting
- Onboarding — Detailed evaluation to establish baseline scores and monitoring requirements
- Periodic review — Annual for all vendors, quarterly for Tier 1 and high-risk vendors
- Trigger-based — After security incidents, ownership changes, regulatory shifts, or scope expansion
The 5 Vendor Risk Categories
Every vendor risk assessment should evaluate five distinct categories. Each captures a different dimension of risk, and a vendor can score well in one category while posing serious concerns in another. A financially stable vendor might have terrible cybersecurity. A compliance-perfect vendor might have reputational issues. You need the full picture.
Category 1: Financial Risk
Financial risk evaluates whether a vendor has the financial stability to fulfill its obligations over the term of your relationship. A vendor that looks healthy today might be overleveraged, losing market share, or burning through cash — any of which could lead to service disruptions, quality cuts, or outright failure.
Why it matters: When a vendor goes under, you lose more than a supplier. You lose continuity, institutional knowledge, and the time it takes to source and onboard a replacement. For critical vendors, a financial failure can cascade through your operations.
What to evaluate:
- Revenue trends (growing, stable, or declining)
- Profitability and margin health
- Debt-to-equity ratio and leverage
- Cash flow adequacy
- Credit ratings (D&B, S&P, Moody's)
- Customer concentration (does one client represent 40%+ of their revenue?)
- Funding status (for startups/growth-stage companies)
- History of mergers, acquisitions, or ownership changes
- Litigation or legal judgments that could affect financial position
- Payment behavior with their own vendors (a leading indicator)
Red flags:
- ❌ Declining revenue for 2+ consecutive years
- ❌ Negative cash flow with no clear path to profitability
- ❌ High customer concentration — losing one client could destabilize them
- ❌ Recent credit rating downgrades
- ❌ Frequent leadership turnover in finance or executive roles
- ❌ Reluctance to share financial information
Category 2: Operational Risk
Operational risk assesses whether a vendor can reliably deliver the products or services you need, at the quality and volume required, consistently over time. This goes beyond "can they do the work?" to "can they do the work when things go wrong?"
Why it matters: Operational failures are the most common vendor risk events. Late deliveries, quality defects, capacity constraints, and key-person dependencies can all disrupt your business — and they tend to happen at the worst possible times.
What to evaluate:
- Delivery track record (on-time delivery percentage)
- Quality metrics (defect rates, rejection rates, first-pass yield)
- Production capacity and utilization rates
- Scalability — can they handle a 50% volume increase?
- Business continuity and disaster recovery plans
- Geographic concentration of operations (single facility vs. distributed)
- Workforce stability and key-person dependencies
- Technology infrastructure and reliability
- Subcontractor dependencies (who do they depend on?)
- Insurance coverage adequacy (general liability, professional liability, workers' comp)
Red flags:
- ❌ On-time delivery below 90%
- ❌ No documented business continuity or disaster recovery plan
- ❌ Single manufacturing facility or data center with no redundancy
- ❌ Heavy reliance on one or two key employees with no succession plan
- ❌ History of quality recalls or service outages
- ❌ Significant dependence on subcontractors they don't control
Category 3: Compliance Risk
Compliance risk examines whether a vendor operates in accordance with applicable laws, regulations, industry standards, and your contractual requirements. In regulated industries, your vendor's compliance failure can become your compliance failure.
Why it matters: Regulators don't care that a violation originated with your vendor. If your vendor mishandles protected health information, your organization faces the HIPAA penalties. If your payment processor doesn't meet PCI-DSS requirements, your organization bears the liability. The regulatory buck stops with you.
What to evaluate:
- Industry-specific certifications (ISO 27001, SOC 2, HIPAA, PCI-DSS, FedRAMP)
- Regulatory compliance history (fines, penalties, consent orders)
- Data handling and privacy practices (GDPR, CCPA, state privacy laws)
- Anti-corruption and anti-bribery policies (FCPA, UK Bribery Act)
- Environmental compliance (EPA regulations, ESG commitments)
- Labor law compliance (OSHA, Fair Labor Standards Act, child labor policies)
- Export control and sanctions compliance (OFAC, EAR, ITAR)
- Accessibility compliance (ADA, WCAG for digital services)
- Contract compliance — are they meeting their SLA obligations?
- Audit rights — does your contract allow you to audit their compliance?
Red flags:
- ❌ Missing or expired industry certifications
- ❌ History of regulatory fines or enforcement actions
- ❌ No documented data privacy or data handling policies
- ❌ Operations in high-corruption-risk jurisdictions without adequate controls
- ❌ Resistance to compliance audits or questionnaires
- ❌ Non-compliance with contractual SLAs without remediation
Category 4: Cybersecurity Risk
Cybersecurity risk evaluates a vendor's ability to protect your data, systems, and networks from unauthorized access, breaches, and attacks. Any vendor with access to your data, systems, or network is a potential attack vector — and threat actors know that vendors are often the weakest link.
Why it matters: The Kaseya, SolarWinds, and MOVEit breaches demonstrated that a single compromised vendor can affect thousands of downstream organizations. Your security is only as strong as the weakest vendor in your ecosystem.
What to evaluate:
- Security certifications and frameworks (SOC 2 Type II, ISO 27001, NIST CSF)
- Data encryption practices (at rest and in transit)
- Access control policies (role-based access, multi-factor authentication, least-privilege principles)
- Vulnerability management program (scanning frequency, patching cadence)
- Incident response plan and breach notification procedures
- Employee security training and awareness programs
- Physical security controls (data centers, offices)
- Third-party security audits and penetration testing results
- Data retention and destruction policies
- Subprocessor management (do they share your data with fourth parties?)
- Remote work security policies and controls
- Cyber insurance coverage
Red flags:
- ❌ No SOC 2 or equivalent security certification
- ❌ No documented incident response plan
- ❌ Data transmitted or stored without encryption
- ❌ No regular penetration testing or vulnerability scanning
- ❌ Lack of multi-factor authentication for system access
- ❌ History of data breaches without demonstrated remediation
- ❌ No cyber insurance coverage
Category 5: Reputational Risk
Reputational risk assesses whether a vendor's public image, ethical practices, or associations could damage your organization's brand, stakeholder trust, or market position. In the era of social media and ESG scrutiny, your vendors' reputations are an extension of your own.
Why it matters: When a vendor is exposed for environmental violations, labor abuses, or ethical failures, the companies that do business with them face public backlash by association. "We didn't know" is not a defense that customers, investors, or regulators accept anymore.
What to evaluate:
- Media coverage and public perception (positive, neutral, negative)
- ESG (Environmental, Social, Governance) track record and commitments
- Labor practices and working conditions (their operations and supply chain)
- Environmental practices and sustainability record
- Ethical business conduct history
- Social media sentiment and customer reviews
- Political associations or controversies
- Diversity, equity, and inclusion practices
- Community engagement and corporate social responsibility
- Leadership conduct and public statements
Red flags:
- ❌ Recent negative media coverage for ethical, environmental, or labor issues
- ❌ No published ESG policy or sustainability commitments
- ❌ Customer complaints and negative reviews indicating systemic issues
- ❌ Active lawsuits alleging discrimination, fraud, or environmental damage
- ❌ Association with sanctioned entities or controversial organizations
- ❌ Leadership involved in public controversies
Vendor Risk Scoring Matrix Template
The scoring matrix is the core of your risk assessment. It transforms subjective judgments into quantifiable scores that enable comparison, prioritization, and tracking over time. Use a 1-5 scale across all five risk categories, weighted by their importance to your organization.
The 1-5 Scoring Scale
| Score | Rating | Definition |
|---|---|---|
| 5 | Very Low Risk | Exceeds all requirements. Demonstrable best-in-class practices. No concerns identified. |
| 4 | Low Risk | Meets all requirements with minor areas for improvement. No material concerns. |
| 3 | Moderate Risk | Meets most requirements but has gaps that need monitoring. Acceptable with controls. |
| 2 | High Risk | Significant gaps identified. Requires remediation plan and enhanced monitoring. |
| 1 | Critical Risk | Major deficiencies. Unacceptable without immediate and substantial remediation. |
Category Weights
Adjust these weights based on your industry, regulatory environment, and risk appetite. The weights below represent a general-purpose starting point.
| Risk Category | Default Weight | Regulated Industry | Technology-Heavy |
|---|---|---|---|
| Financial Risk | 25% | 20% | 20% |
| Operational Risk | 25% | 20% | 20% |
| Compliance Risk | 20% | 30% | 15% |
| Cybersecurity Risk | 20% | 20% | 35% |
| Reputational Risk | 10% | 10% | 10% |
| Total | 100% | 100% | 100% |
Complete Scoring Template
Vendor Risk Assessment Scoring Template
Vendor Name: ___________________________ Assessment Date: ___________________________ Assessed By: ___________________________ Assessment Type: ☐ Pre-qualification ☐ Annual Review ☐ Trigger-based Vendor Tier: ☐ Tier 1 (Strategic) ☐ Tier 2 (Important) ☐ Tier 3 (Commodity)
Financial Risk (Weight: ____%)
Criteria Score (1-5) Notes Revenue stability and growth trends ___ Profitability and margin health ___ Debt levels and leverage ___ Cash flow adequacy ___ Credit rating ___ Customer concentration ___ Financial Risk Average ___ Operational Risk (Weight: ____%)
Criteria Score (1-5) Notes Delivery reliability (on-time %) ___ Quality track record ___ Capacity and scalability ___ Business continuity planning ___ Workforce stability ___ Geographic diversification ___ Operational Risk Average ___ Compliance Risk (Weight: ____%)
Criteria Score (1-5) Notes Required certifications current ___ Regulatory compliance history ___ Data privacy practices ___ Anti-corruption controls ___ Labor and safety compliance ___ Contract/SLA compliance ___ Compliance Risk Average ___ Cybersecurity Risk (Weight: ____%)
Criteria Score (1-5) Notes Security certifications (SOC 2, ISO 27001) ___ Data encryption (at rest and in transit) ___ Access controls and authentication ___ Vulnerability management program ___ Incident response plan ___ Security audit and pen test results ___ Cybersecurity Risk Average ___ Reputational Risk (Weight: ____%)
Criteria Score (1-5) Notes Media coverage and public perception ___ ESG track record ___ Labor and environmental practices ___ Customer reviews and sentiment ___ Leadership conduct ___ Ethical business history ___ Reputational Risk Average ___
Composite Risk Score Calculation
Category Average Score Weight Weighted Score Financial Risk ___ ___% ___ Operational Risk ___ ___% ___ Compliance Risk ___ ___% ___ Cybersecurity Risk ___ ___% ___ Reputational Risk ___ ___% ___ Composite Risk Score ___ / 5.0
Risk Decision
Composite Score Risk Level Action 4.0 - 5.0 Low Risk Approve. Standard monitoring. 3.0 - 3.9 Moderate Risk Approve with conditions. Enhanced monitoring. 2.0 - 2.9 High Risk Conditional approval. Remediation plan required. 1.0 - 1.9 Critical Risk Do not approve. Reassess after remediation. Decision: ☐ Approved ☐ Approved with Conditions ☐ Not Approved Conditions / Remediation Required: ___________________________ Next Assessment Date: ___________________________ Approved By: ___________________________
How to Calculate the Composite Score
The composite score is a weighted average. Here's the formula and an example:
Composite Score = (Financial Avg x Financial Weight)
+ (Operational Avg x Operational Weight)
+ (Compliance Avg x Compliance Weight)
+ (Cybersecurity Avg x Cybersecurity Weight)
+ (Reputational Avg x Reputational Weight)
Example calculation:
| Category | Average Score | Weight | Weighted Score |
|---|---|---|---|
| Financial Risk | 4.2 | 25% | 1.05 |
| Operational Risk | 3.8 | 25% | 0.95 |
| Compliance Risk | 4.5 | 20% | 0.90 |
| Cybersecurity Risk | 2.8 | 20% | 0.56 |
| Reputational Risk | 4.0 | 10% | 0.40 |
| Composite Score | 3.86 / 5.0 |
Interpretation: This vendor scores 3.86 (Moderate Risk). Overall acceptable, but the cybersecurity score of 2.8 is a concern. Action: approve with conditions — require the vendor to submit a cybersecurity remediation plan addressing identified gaps within 60 days, with a follow-up assessment in 90 days.
Risk Assessment Checklists by Category
Use these checklists during each vendor risk assessment to ensure thorough, consistent evaluation. Each item should be verified with documentation, not just vendor self-attestation.
Financial Risk Checklist
Financial Risk Assessment Checklist
Documentation to collect:
- ☐ Annual financial statements (last 3 years) or D&B report
- ☐ Credit report / credit rating
- ☐ Bank references
- ☐ Customer references (to verify payment practices)
- ☐ Proof of insurance coverage (COI)
Evaluation criteria:
- ☐ Revenue has been stable or growing over the past 3 years
- ☐ Company is profitable or has a clear, funded path to profitability
- ☐ Debt-to-equity ratio is within acceptable range (industry-dependent, generally under 2:1)
- ☐ Cash reserves are sufficient to cover at least 3 months of operating expenses
- ☐ No single customer represents more than 30% of revenue
- ☐ Credit rating is satisfactory (D&B score above 70, or equivalent)
- ☐ No material pending litigation or legal judgments
- ☐ No recent bankruptcy, restructuring, or significant leadership turnover
- ☐ Payment terms with their own suppliers are current (not consistently late)
- ☐ Insurance coverage is adequate for the scope of work
Risk-adjusted action:
- Score 4-5: Standard monitoring (annual financial review)
- Score 3: Enhanced monitoring (semi-annual financial review, require financial covenants)
- Score 1-2: Require personal guarantees, payment bonds, or escrow arrangements; identify backup vendor
Operational Risk Checklist
Operational Risk Assessment Checklist
Documentation to collect:
- ☐ Business continuity plan (BCP)
- ☐ Disaster recovery plan (DRP)
- ☐ Quality management certifications (ISO 9001, Six Sigma, etc.)
- ☐ Delivery performance records (last 12 months)
- ☐ Organizational chart showing key personnel
- ☐ List of subcontractors and their roles
Evaluation criteria:
- ☐ On-time delivery rate exceeds 95%
- ☐ Quality defect rate is below 2% (or industry benchmark)
- ☐ Documented business continuity plan has been tested within the past 12 months
- ☐ Disaster recovery plan includes recovery time objectives (RTO) and recovery point objectives (RPO)
- ☐ Operations are not concentrated in a single facility or geography
- ☐ No critical single-person dependencies without succession plans
- ☐ Vendor can demonstrate ability to scale capacity by at least 25-50%
- ☐ Subcontractor dependencies are documented and managed
- ☐ Technology infrastructure has redundancy and failover capabilities
- ☐ Vendor has adequate staffing levels with manageable turnover rates
Risk-adjusted action:
- Score 4-5: Standard monitoring (quarterly performance scorecard)
- Score 3: Enhanced monitoring (monthly performance reviews, require BCP documentation)
- Score 1-2: Require dedicated account team, establish safety stock, activate backup vendor qualification
Compliance Risk Checklist
Compliance Risk Assessment Checklist
Documentation to collect:
- ☐ All required industry certifications (ISO, SOC, HIPAA, PCI-DSS, etc.)
- ☐ Regulatory compliance history (any fines, penalties, or enforcement actions)
- ☐ Data processing agreement (DPA) if handling personal data
- ☐ Privacy policy and data handling procedures
- ☐ Anti-corruption / anti-bribery policy
- ☐ Code of conduct or ethics policy
- ☐ Environmental compliance documentation
Evaluation criteria:
- ☐ All required certifications are current and valid
- ☐ No regulatory fines or enforcement actions in the past 5 years
- ☐ Data privacy practices comply with GDPR, CCPA, and applicable state laws
- ☐ Written anti-corruption and anti-bribery policies are in place and enforced
- ☐ Labor practices comply with all applicable laws (no child labor, fair wages, safe conditions)
- ☐ Environmental practices meet regulatory requirements and your ESG standards
- ☐ Contract includes audit rights allowing you to verify compliance
- ☐ Vendor has a compliance officer or designated compliance function
- ☐ Export control and sanctions screening completed (OFAC, denied party lists)
- ☐ Vendor cooperates fully with compliance questionnaires and audits
Risk-adjusted action:
- Score 4-5: Standard monitoring (annual compliance review, automated document tracking)
- Score 3: Enhanced monitoring (semi-annual compliance review, require corrective action plan)
- Score 1-2: Suspend new work until gaps are remediated; escalate to legal and compliance teams
Cybersecurity Risk Checklist
Cybersecurity Risk Assessment Checklist
Documentation to collect:
- ☐ SOC 2 Type II report (or SOC 1 if applicable)
- ☐ ISO 27001 certification (if applicable)
- ☐ Most recent penetration test results summary
- ☐ Vulnerability scan reports (summary level)
- ☐ Incident response plan
- ☐ Completed security questionnaire (SIG, CAIQ, or custom)
- ☐ Cyber insurance certificate
Evaluation criteria:
- ☐ SOC 2 Type II report is current with no critical findings
- ☐ All data is encrypted at rest and in transit (AES-256 or equivalent)
- ☐ Multi-factor authentication is required for all system access
- ☐ Role-based access control with least-privilege principles is implemented
- ☐ Vulnerability scanning is performed at least monthly
- ☐ Penetration testing is performed at least annually by a qualified third party
- ☐ Documented incident response plan has been tested within the past 12 months
- ☐ Breach notification procedures meet your contractual requirements (typically 24-72 hours)
- ☐ Employee security awareness training is conducted at least annually
- ☐ Vendor has cyber insurance with adequate coverage limits
- ☐ Data retention and destruction policies are documented and followed
- ☐ Subprocessor data sharing is documented and controlled
Risk-adjusted action:
- Score 4-5: Standard monitoring (annual security review, SOC 2 report refresh)
- Score 3: Enhanced monitoring (semi-annual security review, require remediation timeline for gaps)
- Score 1-2: Restrict data access immediately; require security remediation plan with 30-day milestones; consider termination if not resolved within 90 days
Reputational Risk Checklist
Reputational Risk Assessment Checklist
Documentation to collect:
- ☐ ESG report or sustainability commitments
- ☐ Diversity, equity, and inclusion policy
- ☐ Code of ethics / code of conduct
- ☐ Corporate social responsibility report (if available)
- ☐ Media monitoring results (past 12 months)
Evaluation criteria:
- ☐ No significant negative media coverage in the past 24 months
- ☐ No active lawsuits alleging fraud, discrimination, or environmental damage
- ☐ Published ESG commitments with measurable goals and progress reporting
- ☐ Labor practices align with your organization's values and standards
- ☐ Environmental practices meet or exceed regulatory requirements
- ☐ Customer reviews and satisfaction ratings are generally positive
- ☐ Leadership has no personal controversies that could create reputational risk
- ☐ No associations with sanctioned entities or controversial organizations
- ☐ Vendor demonstrates commitment to diversity, equity, and inclusion
- ☐ Vendor engages in community or charitable activities (indicates values alignment)
Risk-adjusted action:
- Score 4-5: Standard monitoring (annual media and reputation review)
- Score 3: Enhanced monitoring (quarterly media monitoring, request vendor response to specific concerns)
- Score 1-2: Engage legal counsel to assess exposure; develop transition plan to alternative vendor; consider contract termination clause activation
How to Automate Vendor Risk Assessments
Manual risk assessments don't scale. If your team is managing 100+ vendors with spreadsheet-based assessments, you're either spending excessive time on the process or cutting corners on thoroughness. Usually both. Vendor portal technology changes this equation fundamentally.
The Problem with Manual Risk Assessment
Manual risk assessments break down in four predictable ways:
- Time drain — A thorough assessment takes 4-8 hours per vendor. With 200+ vendors, that's 800-1,600 hours per year. Most teams don't have that capacity, so assessments get delayed or skipped entirely.
- Consistency gaps — Different team members apply criteria differently. Scoring is subjective without standardized rubrics. Documentation quality varies wildly.
- Tracking failures — Reassessment dates get missed, remediation items aren't followed up, and risk scores go stale when vendor circumstances change.
- Audit challenges — Proving due diligence requires assembling documentation from multiple sources. Assessment history is fragmented with no clear audit trail.
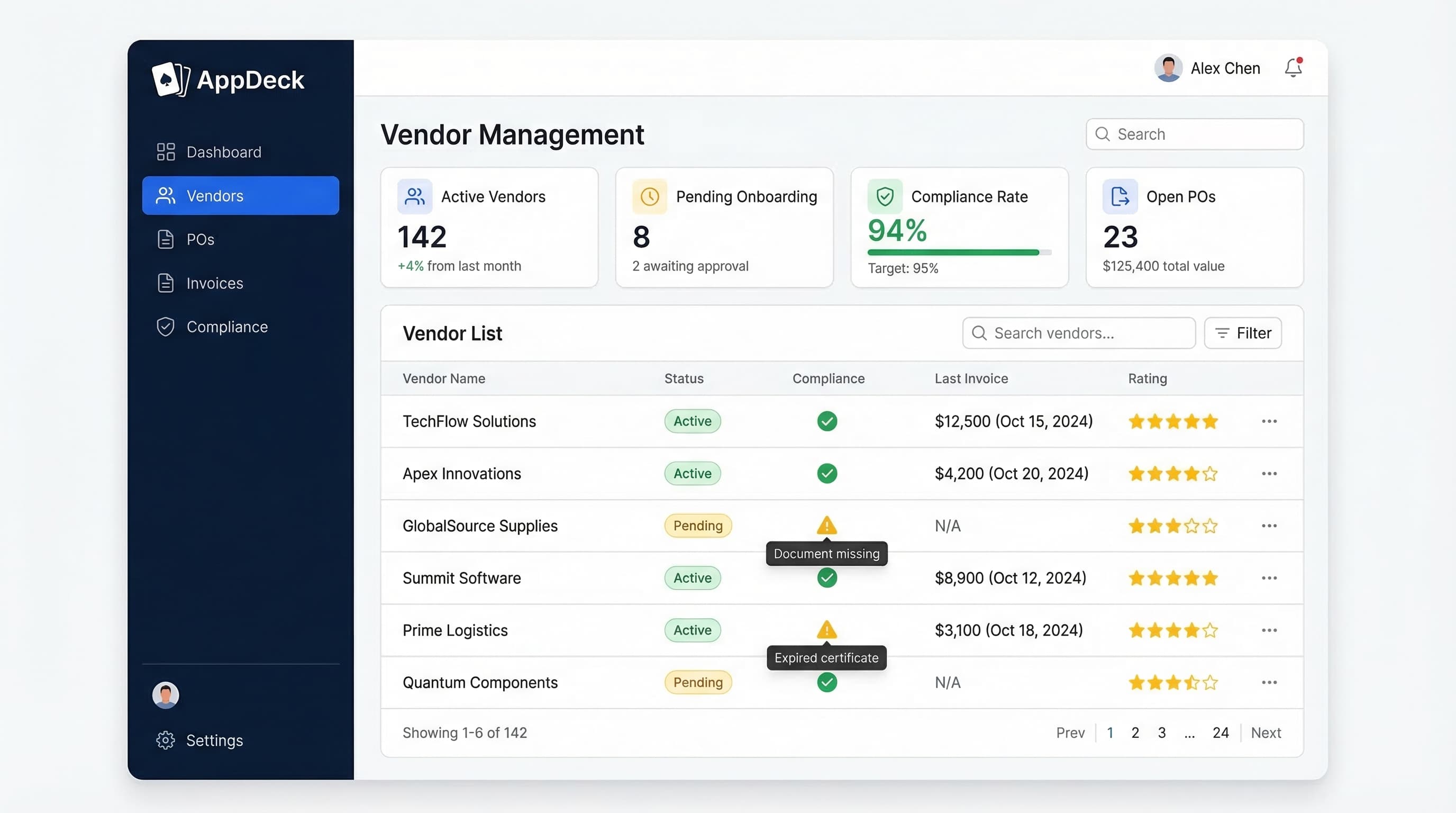
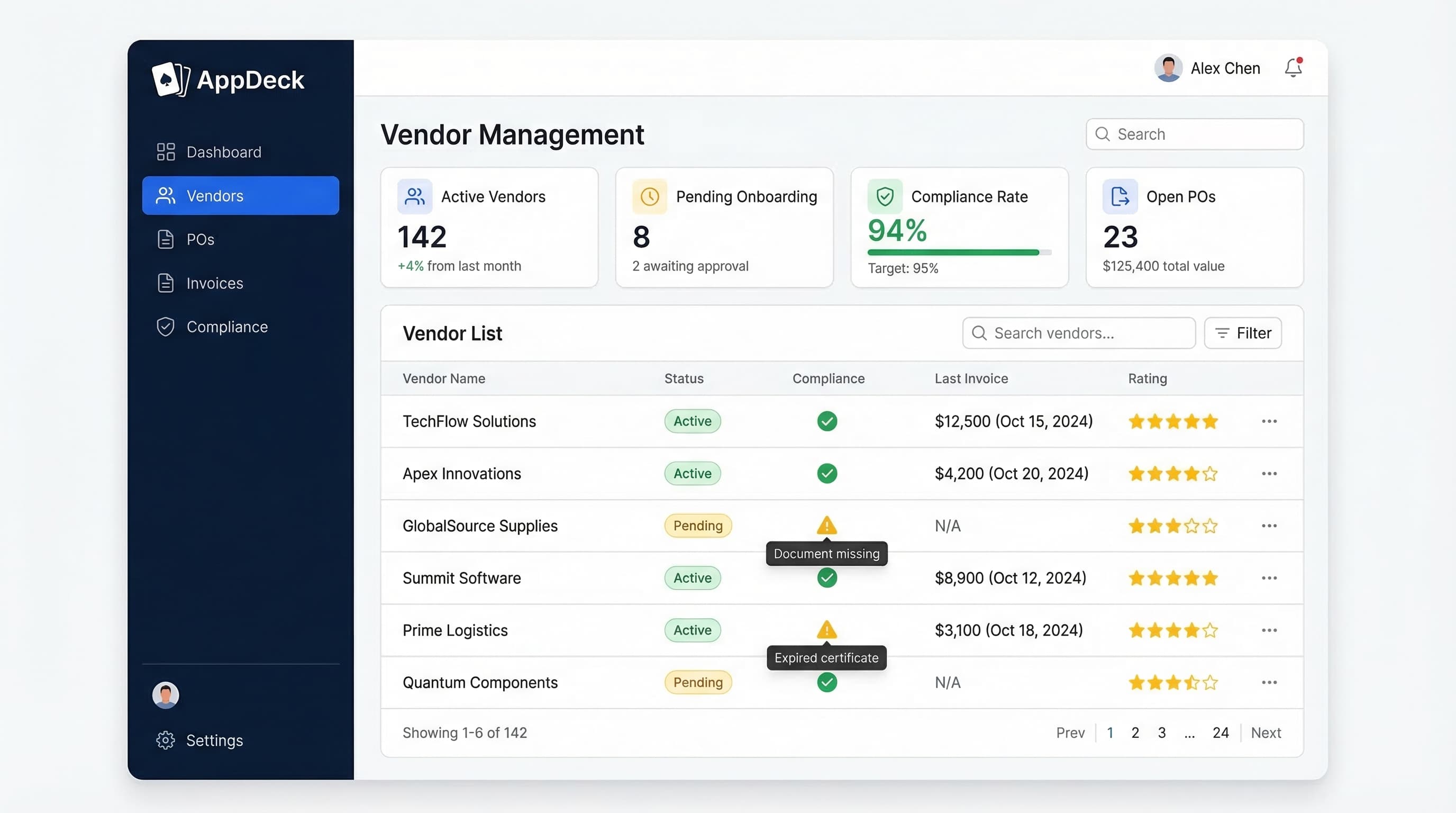
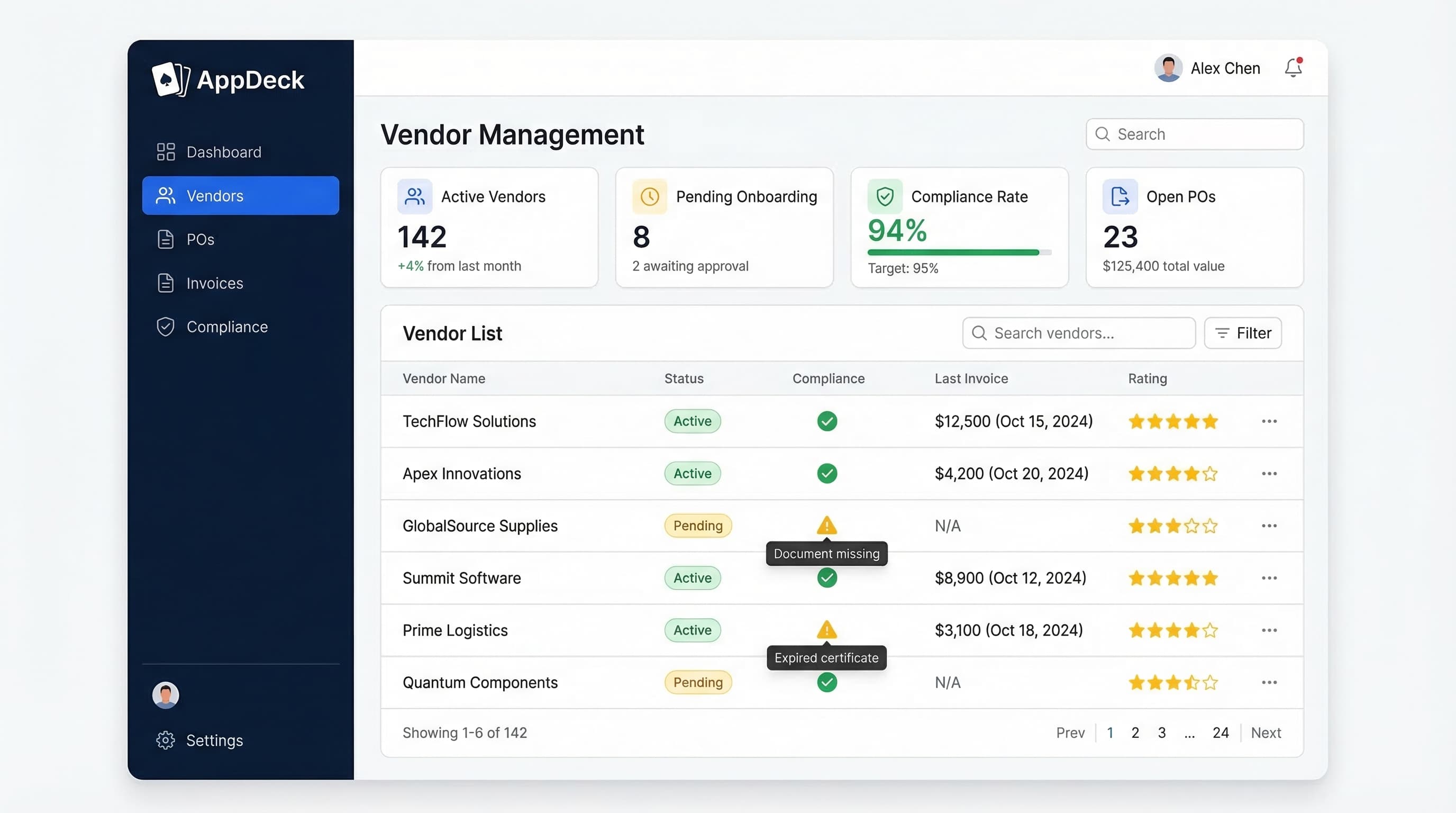
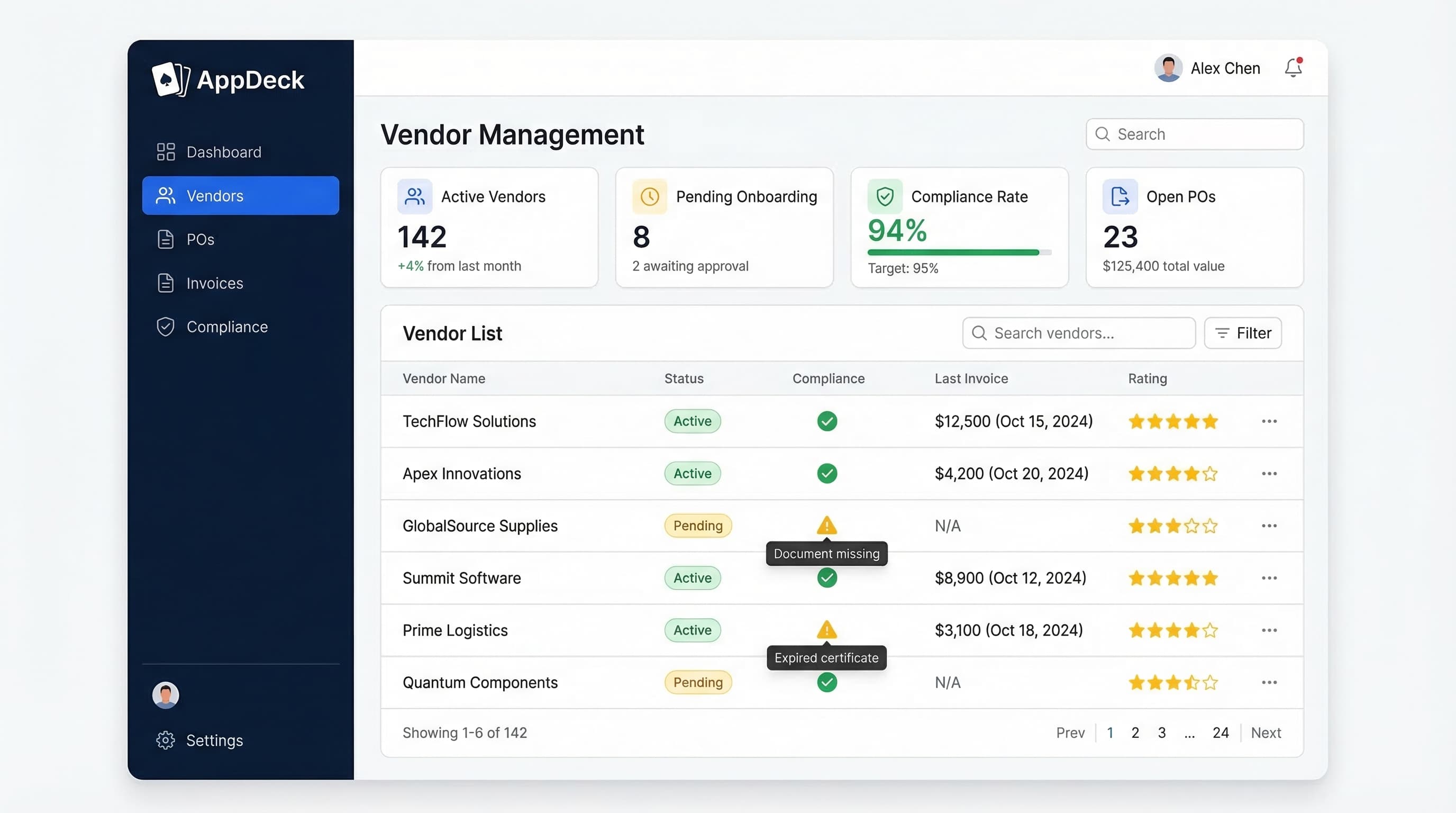
How a Vendor Portal Automates the Process
A vendor portal transforms risk assessment from a periodic, manual project into a continuous, systematic process. Here's how each component works.
Automated document collection — Vendors upload required documents directly through the portal. The system tracks expiration dates, sends automated renewal reminders, and flags missing documents. No manual checking required.
Standardized assessment workflows — Pre-built templates ensure consistent evaluation. Scoring rubrics are embedded so assessors see definitions while scoring. Multi-assessor workflows aggregate scores from subject matter experts across finance, security, and compliance.
Continuous monitoring — Document expirations trigger automatic reassessment requirements. Performance data feeds into operational risk scores in real time. Configurable alerts notify your team when a vendor's risk profile changes. Dashboards show risk distribution across your entire portfolio.
Risk-based vendor tiering — Assessment scores automatically inform tier assignments. Higher-risk vendors get flagged for more frequent reviews. Risk trends over time are visible in vendor profiles.
Audit-ready documentation — Every assessment is timestamped, attributed, and stored with a complete audit trail. One-click export for auditors demonstrates systematic due diligence to regulators.
Implementation Roadmap
If you're moving from no formal risk assessment to a structured, automated process, here's a practical rollout plan:
Phase 1 — Foundation (Weeks 1-2): Adopt the scoring matrix from this guide, define category weights, identify your top 20 vendors for initial assessment, and set up your vendor portal with risk assessment workflows.
Phase 2 — Tier 1 Assessment (Weeks 3-6): Conduct full assessments for your top 20 vendors. Collect documentation through the portal, establish baseline scores, and create remediation plans for high-risk findings.
Phase 3 — Expand to Tier 2 (Weeks 7-12): Extend assessments to the next 30-50 vendors. Refine scoring rubrics based on Phase 2 learnings. Set up automated reassessment schedules and risk monitoring dashboards.
Phase 4 — Full Coverage (Months 4-6): Assess remaining Tier 3 vendors with simplified assessments. Establish an annual assessment calendar, train all team members, and report aggregate risk metrics to leadership quarterly.
Common Vendor Risk Assessment Mistakes
After helping dozens of organizations build risk assessment programs, these are the mistakes I see most frequently.
Mistake #1: Treating it as a one-time exercise. You assess vendors during onboarding, file the results, and never revisit them. Three years later, the vendor's situation has changed dramatically and you have no idea. Fix: Recurring assessment schedules — annual minimum, quarterly for high-risk vendors.
Mistake #2: Relying on vendor self-attestation alone. Vendors check all the right boxes on your questionnaire, but you never verify. When something goes wrong, you discover their answers were aspirational, not actual. Fix: Require documentation for every critical claim — SOC 2 reports, financial statements, penetration test summaries.
Mistake #3: Assessing all vendors with the same intensity. You either waste time on a full cybersecurity review of your office supply vendor or give a cloud provider hosting customer data the same lightweight review as a janitorial service. Fix: Tier your assessments — full five-category for Tier 1, simplified for Tier 3.
Mistake #4: No follow-through on remediation. You identify risks, document them, and nothing changes. Six months later, the same gaps exist. Fix: Every finding above a threshold requires a remediation plan with actions, owners, deadlines, and verification dates — tracked in your vendor portal, not email.
Mistake #5: Ignoring reputational risk. You focus on financial and operational risk because they're quantifiable, while a vendor's ESG controversies create exposure that blindsides you. Fix: Include reputational risk in every assessment. A simple media search and ESG review catches most issues early.
Conclusion
Vendor risk assessment isn't optional — it's a fundamental part of responsible procurement. The organizations that do it well avoid costly surprises, maintain regulatory compliance, and build a vendor portfolio they can trust.
Key takeaways:
- Assess five categories — Financial, operational, compliance, cybersecurity, and reputational risk each tell a different part of the story
- Use a consistent scoring matrix — The 1-5 scale template in this guide enables objective, comparable assessments
- Weight categories to your reality — A healthcare company weights compliance differently than a technology company; adjust the matrix to fit your risk profile
- Verify, don't just ask — Require documentation for every critical claim; self-attestation alone is insufficient
- Reassess continuously — Annual at minimum, quarterly for high-risk vendors, and immediately when trigger events occur
- Automate the process — Manual assessments don't scale; a vendor portal makes the process sustainable
Where to start: If you have no formal risk assessment process today, begin with your top 10 vendors. Use the scoring matrix template and checklists from this guide. Conduct the assessments, identify your biggest exposures, and build from there.
For teams ready to move beyond spreadsheets, AppDeck Vendor Portal provides automated risk assessment workflows, document collection, scoring templates, and continuous monitoring — all in a platform your vendors can use for self-service. Setup takes less than an hour.
Related reading:
- Vendor Scorecard Template — Evaluate and track supplier performance
- Vendor Management Best Practices: Complete Guide for 2026
- The Complete Guide to Vendor Management

Founder & CEO, AppDeck
Serial entrepreneur with 20+ years building B2B software companies. Former executive managing 2,800+ employees across three continents. Vik reviews all AppDeck content for accuracy and practical relevance.
Share this article
Explore Related Solutions
Related Articles
Vendor Compliance Checklist: 30 Items Every Procurement Team Needs
Complete vendor compliance checklist for procurement teams. Track certifications, insurance, licenses, contracts, and regulatory requirements with automated reminders.
Vendor Management Best Practices: Complete Guide for 2026
15 vendor management best practices for procurement teams. Covers onboarding, compliance, performance tracking, risk management, and technology.
Vendor Onboarding Process: Step-by-Step Guide for 2026
Complete vendor onboarding process guide. 7-step framework from initial contact to active vendor status with checklists, timelines, and automation tips.
