Secure Client Portal: The Complete Security Guide for Professional Services
How to build a secure client portal. SOC 2, encryption, access controls, HIPAA compliance, and security checklist for agencies and law firms.
Introduction
Every week, professional services firms share confidential client data over email, Slack, Dropbox, and Google Drive. Tax returns. Legal strategies. Financial projections. M&A targets. Sensitive personal health information.
And every week, some of that data ends up where it shouldn't.
IBM's 2025 Cost of a Data Breach Report puts the average breach cost at $4.88 million—and professional services firms face above-average risk because of the volume and sensitivity of client data they handle. For smaller agencies and consultancies, a single breach can be existential: client lawsuits, regulatory fines, lost business, and a reputation that takes years to rebuild.
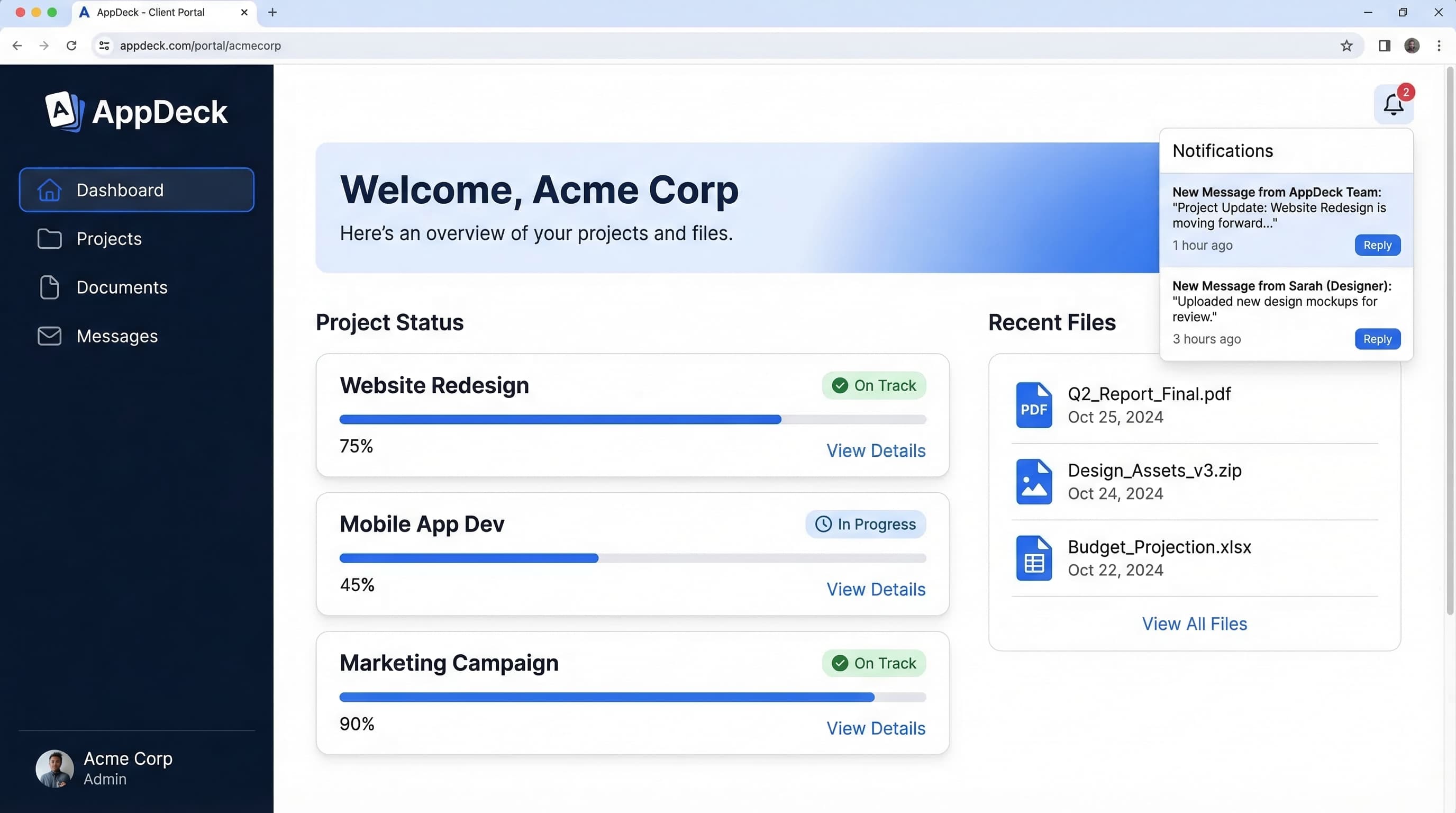
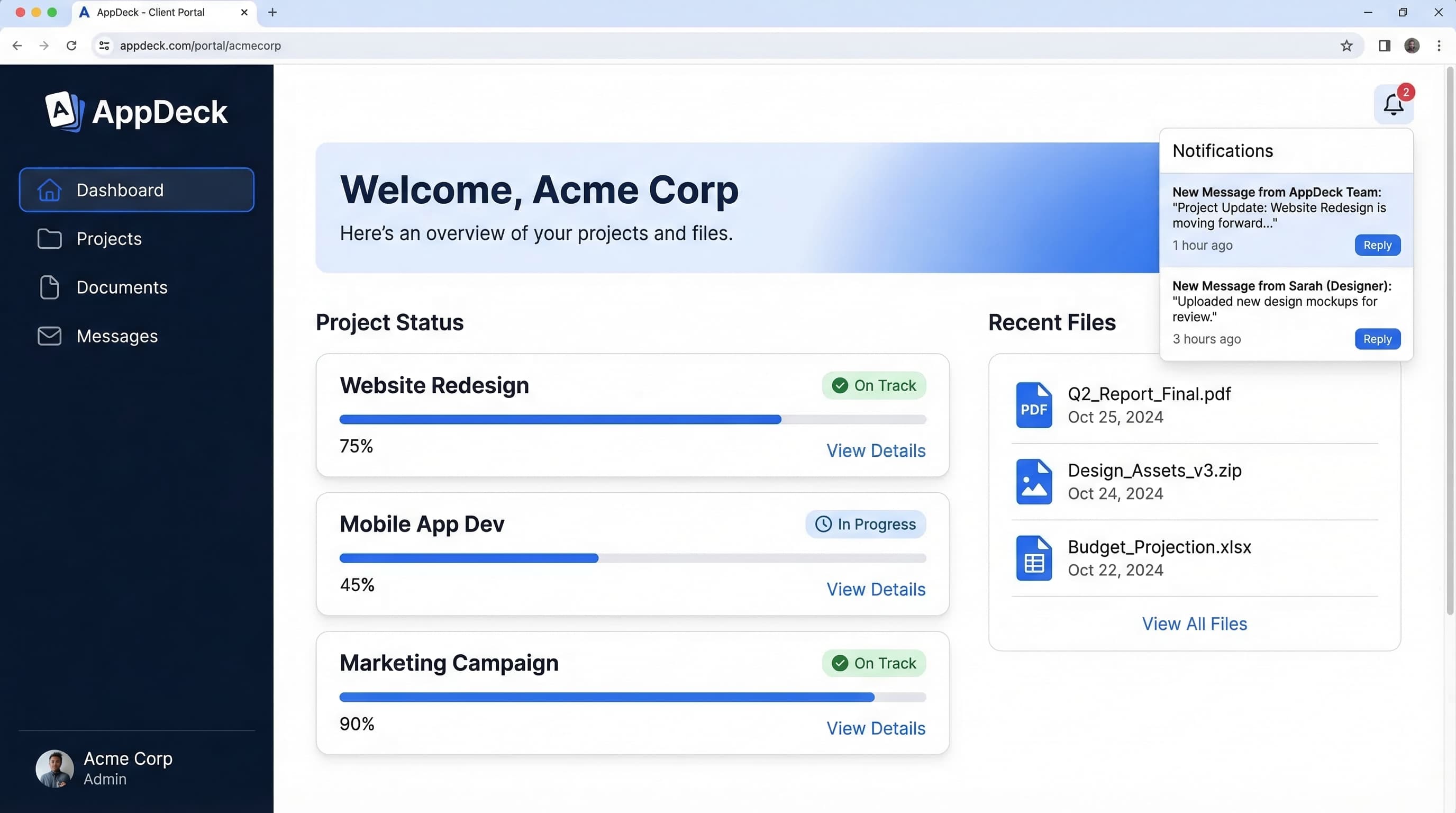
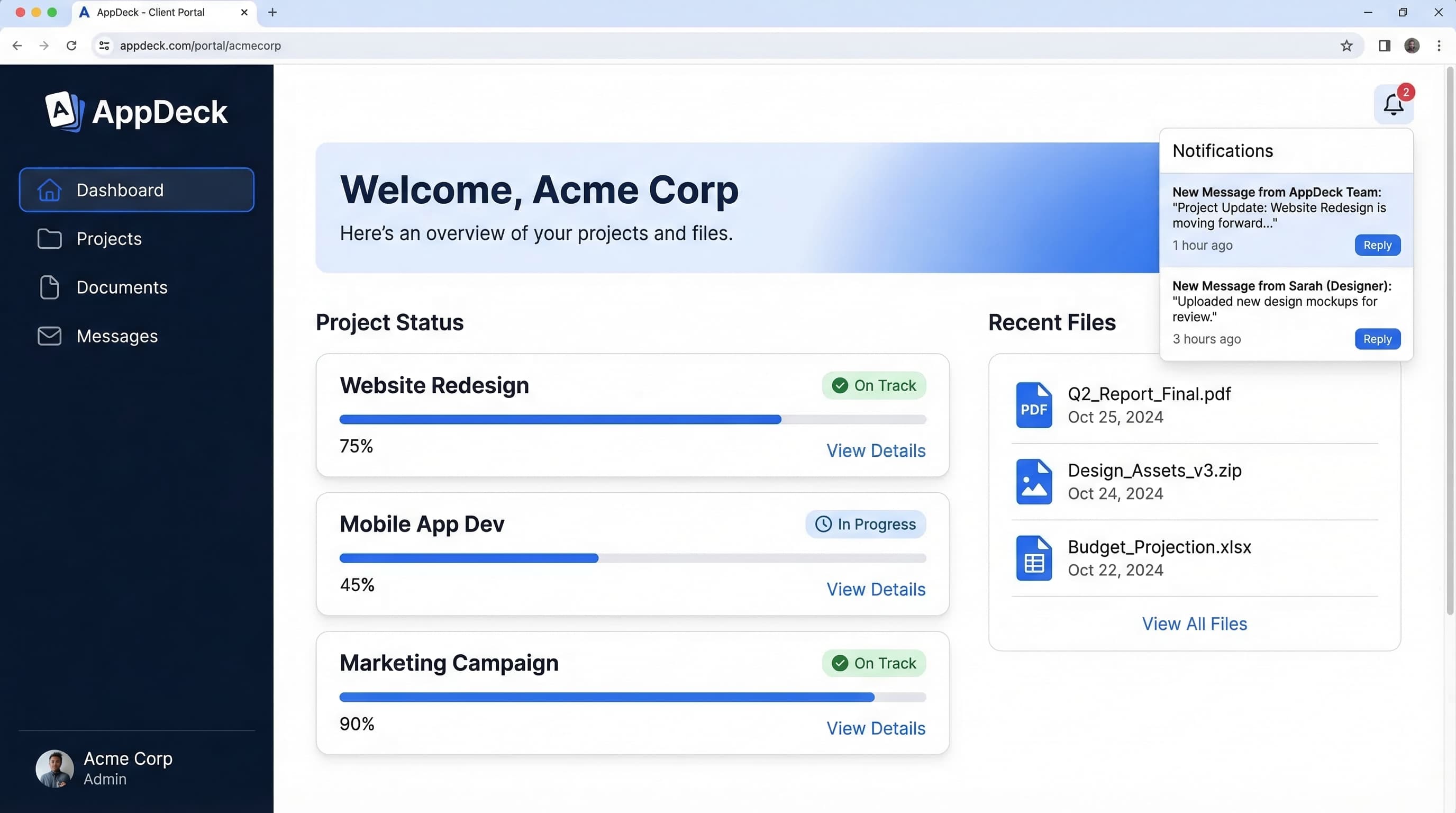
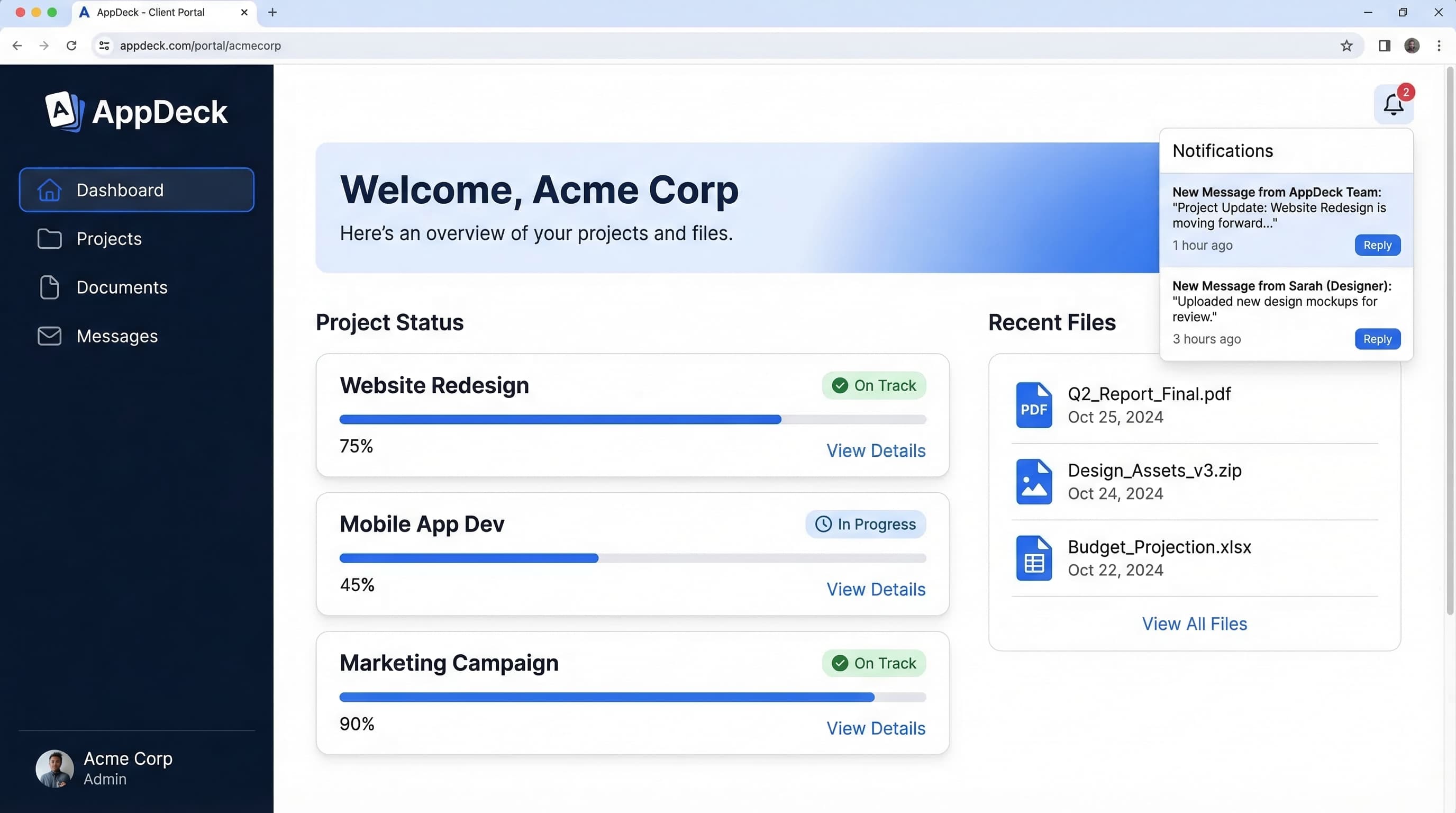
I've spent 20 years building B2B software, and I built AppDeck's client portal specifically because I watched agencies and consultancies struggle with this problem firsthand. They wanted to give clients a better experience than email attachments and shared folders, but they couldn't find a solution that was both easy to use and genuinely secure.
This guide covers everything you need to know about secure client portal software—from encryption standards and compliance certifications to a practical security checklist you can use to evaluate any platform. Whether you're a law firm handling attorney-client privileged communications, a healthcare consultant managing PHI, or a marketing agency protecting client brand assets, this is the security foundation your client portal needs.
What Makes a Client Portal "Secure"?
Most software companies slap a login screen on their product and call it "secure." That's not security. That's a front door.
A truly secure client portal requires multiple overlapping layers of protection, often called "defense in depth." Here's what that actually looks like:
Authentication — Verifying the person is who they claim to be. Username/password alone doesn't cut it anymore. You need multi-factor authentication, SSO integration, and session management.
Encryption — Protecting data both when it's being transmitted (in transit) and when it's stored on servers (at rest). If someone intercepts the data or breaches the server, they get gibberish instead of your client's financial records.
Access Controls — Ensuring people only see what they're authorized to see. Your marketing client shouldn't see your legal client's documents. A junior team member shouldn't see executive compensation data.
Audit Trails — Logging every action: who accessed what document, when, from where, and what they did with it. Without audit trails, you can't detect unauthorized access or prove compliance during a regulatory audit.
Compliance Certifications — Third-party verification that the platform meets specific security standards. SOC 2, ISO 27001, HIPAA—these certifications mean an independent auditor has verified the security controls, not just the vendor's marketing team.
Infrastructure Security — The physical and virtual infrastructure where data lives: server security, network protection, backup systems, disaster recovery. If the data center goes down, your clients' data should survive.
Data Residency — Where your data physically lives matters—especially for firms with international clients subject to GDPR, data sovereignty laws, or sector-specific regulations about cross-border data transfers.
A secure client portal addresses all of these layers. If your current solution is missing any one of them, you have a gap that attackers or regulators will eventually find.
The Client Portal Security Checklist
This is the checklist I use when evaluating secure client portal software. I've organized it into five categories. If you're building or buying a client portal, print this out and check every box.
Encryption
Encryption is your last line of defense. If every other security measure fails—if someone breaches the network, bypasses authentication, and accesses the storage layer—encryption ensures the data they get is worthless.
What to require:
- ✅ AES-256 encryption at rest — The gold standard for stored data. Used by governments and financial institutions worldwide. Your client's documents, messages, and metadata should all be encrypted on disk.
- ✅ TLS 1.3 encryption in transit — The latest transport layer security protocol. All data moving between the client's browser and the server should be encrypted. Reject any platform still using TLS 1.1 or 1.2—they have known vulnerabilities.
- ✅ End-to-end encryption for sensitive documents — For highly confidential files (legal strategies, financial projections, health records), end-to-end encryption ensures even the platform provider can't read the content.
- ✅ Encrypted backups — Backups are often the weakest link. If your primary data is encrypted but your backups aren't, attackers will target the backups. Require AES-256 encryption on all backup copies.
- ✅ Encryption key management — Ask where encryption keys are stored and who has access. Best practice: keys managed through a dedicated key management service (AWS KMS, Azure Key Vault, or GCP Cloud KMS), not stored alongside the data.
Red flags:
- ❌ Vendor can't specify their encryption standards
- ❌ Using outdated protocols (TLS 1.1, SHA-1)
- ❌ Encryption keys stored on the same server as data
- ❌ Backups stored unencrypted "for performance reasons"
Authentication & Access Control
Authentication verifies identity. Access control determines permissions. Together, they ensure the right people see the right data and nobody else.
What to require:
- ✅ Two-factor authentication (2FA) mandatory — Not optional, not "available." Mandatory for all users, including clients. Support for authenticator apps (TOTP), SMS (as a fallback), and hardware keys (FIDO2/WebAuthn).
- ✅ Single sign-on (SSO) — For enterprise clients who use Okta, Azure AD, Google Workspace, or other identity providers. SSO means one less password to manage and centralizes access control with the client's IT team.
- ✅ Role-based access controls (RBAC) — Define roles (admin, team member, client viewer, client editor) and assign granular permissions. A client should only see their own projects. A junior designer shouldn't see financial documents.
- ✅ Session timeout and auto-logout — Inactive sessions should expire after a configurable period (15-30 minutes for sensitive data). No "remember me forever" on shared or public devices.
- ✅ IP whitelisting — For high-security clients, restrict portal access to specific IP ranges. If a law firm's staff should only access the portal from their office network or VPN, enforce that at the platform level.
- ✅ Password policies — Minimum complexity requirements (12+ characters, mixed case, numbers, symbols), password rotation policies, and protection against common/breached passwords (integration with Have I Been Pwned or similar databases).
- ✅ Brute force protection — Account lockout after failed attempts, CAPTCHA on login, and rate limiting to prevent automated attacks.
Red flags:
- ❌ 2FA is "optional" or only available on expensive plans
- ❌ No SSO support (forces enterprise clients to manage another set of credentials)
- ❌ Binary permissions (admin or user, nothing in between)
- ❌ Sessions that never expire
- ❌ No failed login monitoring
Audit & Compliance
For regulated industries—legal, healthcare, financial services, accounting—compliance isn't optional. And even for unregulated agencies, compliance certifications demonstrate security maturity that enterprise clients increasingly require.
What to require:
- ✅ SOC 2 Type II certification — This is the most important certification for SaaS platforms. SOC 2 Type II means an independent auditor observed the company's security controls over a period of 6-12 months and verified they actually work. Type I is a point-in-time snapshot; Type II is ongoing proof. AppDeck is built with a security-first architecture and we're designing for SOC 2 Type II audit readiness — we believe every secure client portal should hold this certification.
- ✅ Complete audit logs — Every action logged: document views, downloads, edits, permission changes, login attempts (successful and failed), and administrative changes. Logs should be immutable (can't be edited or deleted) and retained for a minimum of 1 year.
- ✅ GDPR compliance — If you work with European clients or handle EU citizens' data: data subject access requests, right to deletion, data processing agreements (DPA), consent management, and data portability.
- ✅ HIPAA compliance — If you handle protected health information: Business Associate Agreements (BAA), PHI access logging, minimum necessary access principle, and breach notification procedures. More on this in the industry-specific section below.
- ✅ Data residency controls — Choose where your data is physically stored (US, EU, UK, Australia, etc.). Critical for compliance with data sovereignty laws and client contractual requirements.
- ✅ Penetration testing — Annual penetration testing by qualified third-party security firms, at minimum. Ask for the date of the last pen test and whether critical findings were remediated. Best-in-class platforms run quarterly pen tests and continuous vulnerability scanning.
Red flags:
- ❌ "SOC 2 compliant" without actual certification (compliant ≠ certified)
- ❌ Audit logs that can be edited or have gaps
- ❌ No GDPR-specific features despite handling international data
- ❌ Refuses to sign a BAA for HIPAA
- ❌ Hasn't conducted a penetration test in the last 12 months
Document Security
Documents are usually the most sensitive data in a client portal. Contracts, financial statements, legal briefs, strategic plans—these need protection beyond basic access controls.
What to require:
- ✅ Dynamic watermarking — Automatically overlay the viewer's name, email, and timestamp on viewed documents. If someone screenshots or photographs a document, you know exactly who leaked it.
- ✅ Download restrictions — View-only mode that prevents downloading, printing, or copy-paste. Essential for sensitive documents where you need to share information but maintain control.
- ✅ Expiring links — Shared links that automatically expire after a set time period or number of views. No more "live forever" links floating around in old emails.
- ✅ Remote access revocation — Instantly revoke a user's access to all documents when a project ends, a client relationship terminates, or an employee leaves. Access should be severable in seconds, not days.
- ✅ Version control with change tracking — Every version of every document is preserved. See who changed what, when, and why. Critical for legal and compliance purposes.
- ✅ Secure file types — Support for secure document formats (encrypted PDFs) and scanning uploaded files for malware before they're accessible to other users.
Red flags:
- ❌ No watermarking capability
- ❌ All shared links are permanent
- ❌ Revoking access requires contacting support
- ❌ No version history (deleted means gone)
- ❌ No malware scanning on uploads
Infrastructure
The most secure application in the world is worthless if it's running on a compromised server, an unreliable host, or a provider with no disaster recovery plan.
What to require:
- ✅ SOC 2 compliant hosting — Your portal should run on enterprise-grade infrastructure: AWS, Google Cloud Platform, or Microsoft Azure. These providers invest billions in physical security, network security, and compliance.
- ✅ 99.9%+ uptime SLA — Minimum 99.9% uptime guarantee backed by financial penalties (SLA credits). Calculate the cost of downtime for your clients: 99.9% still means up to 8.7 hours of downtime per year.
- ✅ Automated backups — Daily automated backups at minimum, with point-in-time recovery capability. Backups should be stored in a geographically separate location from the primary data.
- ✅ Disaster recovery plan — Documented, tested disaster recovery procedures with defined Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO). Ask when the DR plan was last tested.
- ✅ DDoS protection — Enterprise-grade DDoS mitigation (Cloudflare, AWS Shield, or equivalent). A DDoS attack shouldn't take down your client portal.
- ✅ Network segmentation — Client data should be logically isolated. One client's data breach shouldn't expose another client's data.
- ✅ Vulnerability management — Continuous vulnerability scanning, timely patching of dependencies, and a responsible disclosure program for security researchers.
Red flags:
- ❌ Hosting on unknown or budget providers
- ❌ No published uptime SLA
- ❌ Backups are "manual" or "periodic"
- ❌ No disaster recovery plan (or one that's never been tested)
- ❌ Single point of failure architecture
Security Requirements by Industry
Different industries face different regulatory requirements. Here's what to prioritize based on your practice area.
Law Firms
Law firms handle attorney-client privileged communications—some of the most legally protected data that exists. A security breach doesn't just expose data; it can waive privilege, create malpractice liability, and violate ethical obligations.
Specific requirements:
- Ethical walls (information barriers) — Prevent team members working on one matter from accessing another matter's data. Essential when your firm represents parties with potentially conflicting interests.
- Attorney-client privilege protections — Access controls that maintain privilege. If privileged documents become accessible to unauthorized parties, privilege may be waived—permanently.
- Bar association compliance — ABA Model Rules 1.1 and 1.6 require lawyers to make "reasonable efforts" to prevent unauthorized disclosure. A secure client portal with audit trails is one of the strongest demonstrations of reasonable effort.
- Litigation hold capability — Ability to preserve and lock specific documents and communications when litigation is anticipated. Prevents spoliation and complies with preservation obligations.
- Matter-level permissions — Each legal matter should be an isolated container. Clients see only their matters. Attorneys see only matters they're assigned to.
Healthcare
Any firm handling protected health information (PHI)—healthcare consultancies, medical billing companies, health tech vendors—must comply with HIPAA.
Specific requirements:
- Business Associate Agreement (BAA) — Your portal vendor must sign a BAA. No BAA = no HIPAA compliance. Period. If a vendor hesitates or doesn't offer one, walk away.
- PHI access logging — Every access to PHI must be logged with the who, what, when, and where. These logs must be retained for 6 years under HIPAA.
- Minimum necessary standard — Access controls must enforce the "minimum necessary" principle: users only access the minimum PHI required for their role.
- Breach notification — The platform must support HIPAA's 60-day breach notification requirement with incident detection and reporting capabilities.
- De-identification support — Ability to strip identifying information from documents when sharing with parties who don't need to see PHI.
If you work with healthcare clients and your current portal isn't HIPAA compliant, you're carrying significant liability. This is non-negotiable.
Financial Services
SEC-regulated firms, FINRA members, and companies subject to SOX have stringent record-keeping and security requirements.
Specific requirements:
- SEC/FINRA record retention — Communications and documents must be retained per regulatory schedules (typically 3-6 years depending on type). The portal must support retention policies and legal holds.
- SOX compliance — For public companies: internal controls over financial reporting. Audit trails, access controls, and change management for any system handling financial data.
- Material non-public information (MNPI) controls — Strict access controls to prevent insider trading. Information barriers between teams handling public and non-public information.
- Client reporting security — Financial reports and statements must be delivered securely with authentication, not as email attachments.
Accounting Firms
Accounting firms handle some of the most sensitive financial data for individuals and businesses: tax returns, financial statements, payroll records, and social security numbers.
Specific requirements:
- SOC 2 certification — For accounting firms, SOC 2 is practically a prerequisite for working with enterprise clients. Your portal vendor should be certified, and you should use that to strengthen your own compliance posture.
- Tax season scalability — The portal must handle seasonal spikes in document uploads and downloads without performance degradation or security shortcuts.
- IRS compliance — For firms handling tax data: compliance with IRS Publication 4557 (Safeguarding Taxpayer Data) and FTC Safeguards Rule requirements.
- Client document requests — Secure, trackable document request workflows that replace email-based "please send us your W-2" exchanges.
Agencies
Marketing, creative, and consulting agencies face different but equally important security challenges—primarily around client NDAs, competitive intelligence, and brand asset protection.
Specific requirements:
- Client NDA compliance — Your portal must enforce the NDAs you've signed. If you've agreed that client data won't be accessible to third parties, your portal's access controls must guarantee that.
- Brand asset protection — Logos, brand guidelines, campaign creative, and strategy documents are high-value intellectual property. View-only access, watermarking, and download restrictions protect assets from unauthorized distribution.
- Competitive separation — If you work with competing clients in the same industry, strict data isolation ensures Client A's strategy never leaks to Client B. This is your ethical obligation and a contractual requirement.
- Freelancer and contractor access — Agencies rely on external talent. The portal must support granular, time-limited access for contractors who need to see specific project files without gaining access to the broader client account.
For a deeper dive into agency-specific portal features beyond security, see our guide on client portal software for agencies.
Secure vs. Insecure Client Portals
I see firms making the same mistakes repeatedly. Here's a direct comparison between common insecure practices and what a secure client portal actually looks like.
Email Attachments vs. Secure Client Portal
- ❌ Email: Documents sit in multiple inboxes indefinitely, unencrypted, searchable, forwardable
- ❌ Email: No access controls—anyone with the email can view attachments
- ❌ Email: No audit trail—you don't know if the attachment was forwarded to 50 people
- ❌ Email: Vulnerable to phishing and email account compromise
- ❌ Email: Can't revoke access after sending
- ✅ Portal: Documents encrypted at rest and in transit
- ✅ Portal: Granular access controls—only authorized users see specific documents
- ✅ Portal: Complete audit trail of every view, download, and share
- ✅ Portal: 2FA protects against credential compromise
- ✅ Portal: Instantly revoke access at any time
Dropbox/Google Drive vs. Purpose-Built Client Portal
- ❌ Generic cloud storage: Not SOC 2 certified for client data use cases
- ❌ Generic cloud storage: Shared links can be forwarded and accessed by anyone
- ❌ Generic cloud storage: No client-specific branding—clients see your messy folder structure
- ❌ Generic cloud storage: No dynamic watermarking on documents
- ❌ Generic cloud storage: Limited audit trails (who accessed what is unclear)
- ❌ Generic cloud storage: No HIPAA BAA available (Google Drive offers one, Dropbox has limitations)
- ✅ Client portal: SOC 2 certified platform purpose-built for client data
- ✅ Client portal: Authenticated access only—no anonymous link sharing
- ✅ Client portal: White-labeled with your brand—clients see a professional, branded experience
- ✅ Client portal: Dynamic watermarking on sensitive documents
- ✅ Client portal: Complete, immutable audit logs
- ✅ Client portal: HIPAA-ready with BAA support
Shared Drives vs. Permissioned Access
- ❌ Shared drives: Everyone on the team sees everything—no granularity
- ❌ Shared drives: Former employees retain access until IT manually removes them
- ❌ Shared drives: No concept of "client A can't see client B's data"
- ❌ Shared drives: Versioning is inconsistent—"Contract_v3_FINAL_FINAL.pdf"
- ✅ Client portal: Role-based permissions at the project and document level
- ✅ Client portal: Access automatically revoked when users are deactivated
- ✅ Client portal: Complete data isolation between clients
- ✅ Client portal: Automatic version control with change tracking
The pattern is clear: generic file-sharing tools trade security for convenience. A secure client portal gives you both.
How to Evaluate Client Portal Security
When you're comparing secure client portal software, these are the questions to ask vendors—and the answers that should concern you.
Questions to Ask Every Vendor
Encryption and Data Protection:
- What encryption standard do you use at rest and in transit?
- Where are encryption keys stored and who has access to them?
- Are backups encrypted with the same standard as primary data?
- Do you support end-to-end encryption for documents?
Compliance and Certification: 5. Are you SOC 2 Type II certified? (Ask for the report, not just a badge.) 6. When was your last penetration test? Can you share a summary of findings? 7. Will you sign a BAA for HIPAA compliance? 8. Where is data physically stored and can I choose the region?
Access Controls: 9. Is 2FA mandatory or optional? Is it available on all plans? 10. Do you support SSO with our identity provider? 11. How granular are your role-based access controls? 12. What happens to a user's access when I deactivate their account?
Incident Response: 13. What's your incident response plan and SLA for security incidents? 14. How quickly do you notify customers of a breach? 15. Do you carry cyber liability insurance?
Red Flags That Should Disqualify a Vendor
- "We're SOC 2 compliant" — Compliant means they follow the principles. Certified means an auditor verified it. If they can't produce a SOC 2 Type II report, they're not certified.
- "Security is on our roadmap" — If basic security features aren't implemented today, don't bet your client data on their roadmap.
- "We've never had a breach" — Either they have robust monitoring and can prove it, or they lack the monitoring to detect breaches. Ask how they know.
- "2FA is available on our Enterprise plan" — Security shouldn't be a premium feature. If basic protections like 2FA are paywalled, the vendor doesn't prioritize security.
- "We handle security, you don't need to worry about it" — Vague answers about security are the biggest red flag. Legitimate security-focused vendors are transparent and specific.
Certifications Worth Requiring
For most professional services firms, this is the certification hierarchy:
- SOC 2 Type II — Required. Non-negotiable for any platform handling client data.
- ISO 27001 — Strong indicator of mature security practices. Common for international platforms.
- HIPAA (with BAA) — Required if handling any healthcare data.
- SOC 1 / SSAE 18 — Relevant if the portal handles financial reporting data.
- FedRAMP — Required for government contracts.
At AppDeck, we're designing for SOC 2 Type II audit readiness from day one because we know professional services firms require it. It's table stakes for any encrypted client portal handling confidential data.
Building a Security-First Client Portal
Whether you're switching from email and spreadsheets or replacing an insecure portal, here's the step-by-step process for setting up a secure client portal the right way.
Step 1: Choose a SOC 2 Certified Platform
Start with the non-negotiable: your platform must be SOC 2 Type II certified. This eliminates the majority of tools on the market and narrows your evaluation to vendors who take security seriously.
AppDeck's client portal is built with AES-256 encryption, 2FA, RBAC, and complete audit logging built in—not bolted on as an afterthought—and we're designing for SOC 2 Type II audit readiness.
Step 2: Configure Multi-Factor Authentication
Enable 2FA for every user—internal team members and external clients. Yes, some clients will push back. Here's how to handle it:
- Frame it as protecting their data, not inconveniencing them
- Offer authenticator app or SMS options
- Provide a simple setup guide (takes 60 seconds)
- Position it as a reflection of your firm's professionalism
In my experience, once you explain that 2FA protects their confidential data, 95% of clients comply without complaint. The other 5% comply after you remind them about recent data breaches in the news.
Step 3: Set Up Role-Based Access Controls
Define your roles before you start adding users:
- Admin — Full access to all clients, settings, and security configuration
- Team Lead — Access to assigned clients' data, can manage team member permissions
- Team Member — Access to assigned projects only, can upload and comment
- Client Owner — Access to their projects and documents, can invite other client users
- Client Viewer — Read-only access to shared documents and reports
- Contractor — Time-limited access to specific project files
Map every person who will use the portal to a role. When in doubt, give less access. You can always grant more.
Step 4: Enable Audit Logging
Turn on comprehensive audit logging from day one. Configure:
- Log retention period (minimum 1 year, ideally 3+ years for regulated industries)
- Alert triggers for suspicious activity (multiple failed logins, unusual download volumes, access from new locations)
- Regular audit log reviews (monthly for most firms, weekly for high-security environments)
Step 5: Test with Your Security Team
Before going live with clients:
- Have your IT team or a security consultant review the configuration
- Test access controls by logging in as different roles and verifying permissions
- Attempt common attack vectors: password guessing, link sharing, permission escalation
- Verify that audit logs capture all test activities accurately
- Document the security configuration for compliance records
Step 6: Document for Clients
Create a brief security overview document that you share with clients during onboarding. This isn't optional—it builds trust and reduces questions. More on this in the next section.
Client-Facing Security Documentation
One of the most underused trust-building tools in professional services is proactive security communication. Don't wait for clients to ask about security—tell them upfront.
What to Share with Clients
Security overview page — A public-facing page on your website that explains how you protect client data. Include your encryption standards, compliance certifications, and infrastructure details. If your portal vendor has a security page, reference it alongside your own practices.
SOC 2 report summary — You can't share the full SOC 2 report with everyone (it contains detailed control descriptions), but you can share a summary or the auditor's opinion letter under NDA. This is the single most persuasive document you can share with security-conscious clients.
Data processing agreement (DPA) — For GDPR compliance, have a standard DPA ready for European clients. Don't make them ask for it—include it in your onboarding materials.
Incident response overview — A brief description of what happens if there's a security incident: how you'll notify clients, what remediation steps you'll take, and your timeline commitments.
Vendor security questionnaire responses — Enterprise clients will send you security questionnaires. Having a pre-completed, up-to-date questionnaire saves weeks of back-and-forth.
Why This Matters
I've won multiple enterprise clients specifically because we could provide SOC 2 documentation and a detailed security overview before they even asked. It signals that you take security as seriously as they do.
The same security standards that protect client data in our portals also protect board communications and investor data rooms—because we believe every confidential interaction deserves enterprise-grade security.
Frequently Asked Questions
What is a secure client portal?
A secure client portal is an authenticated, encrypted platform where professional services firms share documents, communications, and project updates with clients. Unlike email or generic file sharing, a secure client portal provides layered security including AES-256 encryption, two-factor authentication, role-based access controls, complete audit trails, and compliance certifications like SOC 2.
What's the difference between SOC 2 Type I and Type II?
SOC 2 Type I is a point-in-time assessment—an auditor evaluates your security controls on a specific date. SOC 2 Type II is an ongoing assessment over 6-12 months, verifying that controls are not only designed properly but are consistently operating effectively. Type II is significantly more rigorous and is what enterprise clients expect. AppDeck is designing for SOC 2 Type II audit readiness.
Do I need a HIPAA-compliant client portal?
If you handle any protected health information (PHI)—even indirectly—you likely need HIPAA compliance. This applies to healthcare consultants, medical billing companies, health tech vendors, healthcare law firms, and any firm whose clients are healthcare organizations. The portal vendor must sign a Business Associate Agreement (BAA).
How is a client portal more secure than email?
Email is fundamentally insecure for confidential data: messages sit unencrypted in multiple inboxes, can be forwarded without your knowledge, have no access revocation, and lack audit trails. A secure client portal encrypts data at rest and in transit, requires authentication for every access, logs all activity, and lets you revoke access instantly. It's the difference between mailing a document and storing it in a vault with a visitor log.
What encryption should a client portal use?
At minimum: AES-256 encryption for data at rest and TLS 1.3 for data in transit. For highly sensitive documents, look for end-to-end encryption where even the platform provider cannot read the content. Encryption keys should be managed through dedicated key management services (AWS KMS, Azure Key Vault), not stored alongside the data.
Can I use Dropbox or Google Drive as a client portal?
You can, but you shouldn't—at least not for sensitive client data. Generic file-sharing tools lack purpose-built security features like dynamic watermarking, granular role-based access, complete audit trails, and compliance certifications. They also present an unprofessional experience: clients see your folder structure rather than a branded portal experience.
How do I get clients to adopt 2FA?
Frame it as protecting their data, not complicating their login. Provide a simple setup guide, offer authenticator app and SMS options, and make it part of your onboarding process rather than a separate request. In my experience, explaining that "this protects your confidential data the same way your bank protects your account" gets near-universal compliance.
What should I do if my current portal isn't secure enough?
Start by auditing your current platform against the security checklist in this guide. Identify gaps—especially in encryption, 2FA, audit logging, and compliance certifications. If the gaps are fundamental (no SOC 2 certification, no 2FA support, no audit logs), you need to switch platforms. If the gaps are configuration issues, fix them immediately. For a detailed comparison of client portal software options for agencies, see our companion guide.
Next Steps
Client portal security isn't a feature you enable once and forget. It's an ongoing practice: regular audits, updated configurations, vendor assessments, and client communication.
If you're using email, Dropbox, or an insecure tool to share confidential client data, the risk compounds every day. The question isn't whether you'll face a security incident—it's when.
Start with the security checklist above. Evaluate your current tools honestly. And if you're ready to move to a security-first platform built specifically for secure document sharing, explore AppDeck's client portal.
Related Reading

Founder & CEO, AppDeck
Serial entrepreneur with 20+ years building B2B software companies. Former executive managing 2,800+ employees across three continents. Vik reviews all AppDeck content for accuracy and practical relevance.
Share this article
Explore Related Solutions
Related Articles
Client Onboarding Portal: How to Build One That Reduces Time-to-Value by 50%
Learn how to build a client onboarding portal that automates intake, collects documents, and gets clients to value faster. Step-by-step guide with examples and tool recommendations.
12 Client Portal Examples: Real Designs That Impress Clients
12 client portal examples from agencies, accounting firms, law firms, and consultants. See real portal designs with features, layouts, and what makes each one effective.
Client Portal Software for Agencies: Features, Pricing & Comparison (2026)
Compare the best client portal software for agencies. Features, pricing, and real reviews of top platforms to reduce status meetings and improve client communication.
